A railway signaling system is used to direct railway traffic and keep trains clear of each other at all times.
Trains move on fixed rails, making them uniquely susceptible to collisions. This susceptibility is increased by the enormous weight and inertia of a train, which makes it difficult to stop when encountering an obstacle.
Most forms of train control involve “movement authority” being passed from the signalman (or stationmaster) to the crow on the train. The set of rules and the physical equipment used to accomplish this are known as the “method of working” (UK), method of operation (US), or safe working (Aus.).
Here are some of the main Railway signaling systems:
1. ALSN (Russian Federation, Belarus, Estonia, Latvia, Lithuania, Ukraine)
2. ASFA (Spain)
3. ATC (Sweden, Denmark, Norway, Brazil, South Korea, Japan, Australia (Queensland), Indonesia)
4. ATP (United Kingdom, United States of America, Brazil, Australia (Queensland), Indonesia, Hong Kong, Dominican Republic)
5. CBTC (Brazil, United States of America, Canada, Singapore, Spain, Gabon, Hong Kong)
6. PZB Indusi (Germany, Austria, Romania, Slovenia, Croatia, Bosnia-Herzegovina, Serbia, Montenegro, Macedonia, Israel)
What is ETCS?
The European Train Control System (ETCS) is the signaling and control component of the European Rail Traffic Management System (ERTMS). It is intended to replace the legacy train protection systems and the many incompatible safety systems, currently used by European railways. This standard (ETCS) is also adopted outside the EU and is considered to be an option, for worldwide applications.
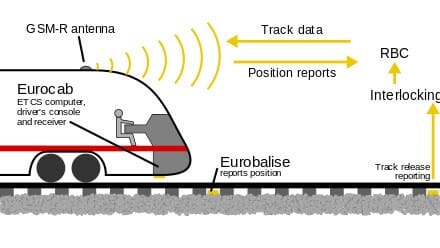
ERTM S uses GSM-R (or GSM for Railway) as the international wireless communications standard for railway communication and applications. GSM-R is typically implemented using dedicated base stations close to the railway, with tunnel coverage affected using directional antennae or ‘leaky’ feeder transmission.
Cyber and Railway signaling systems
Until recently, the operation of railway signaling systems has been considered to be performed using closed networks, and this was the base assumption for the safety of the signaling systems.
Recently, these systems are getting more and more centralized and integrated, thus the assumption that the signaling system is operated within closed networks is no longer sustainable.
At the same time, railway signaling systems have become more and more IT-based, providing functionality that does not only use dedicated computers and hardware but instead uses regular computers and COTS (Commercial off-the-shelf) components, which are more vulnerable to cyber threats. In addition, we see the increased use of networked control and automation systems that can be accessed remotely via public and private networks.
All these “cyber threats” are requiring new measures and efforts in order to ensure the integrity and safety of the railway system.
Some recent examples of cyber-attacks on Railway systems include:
1. Intrusion into the Lodz tram point control system (2009).
2. Deactivating the ticketing system in San Francisco´s public transport system (MUNI, 2016).
3. The so-called “Wannacry” attack in May 2017, infected more than 200,000 computers worldwide, including passenger information screens at railway stations.
An information monitor at a German train station displays the ransomware message Credit: @Zeichen Taten/Twitter
The effects of a successful cyberattack on railway signaling systems
As was described in this article, and shown in recent attacks, railway systems are becoming much more vulnerable to cyber-attacks.
Access to these systems can be gained remotely, via the Internet or the GSM-R channel, through direct contact with the signaling system infrastructure, or by an insider threat.
Successful cyber-attacks in Railway signaling systems could result in:
1. Threats to people’s safety
2. Disruption to the rail network and services
3. Economic loss to rail operators, suppliers, or the wider economy
4. Reputation damage to rail companies
5. Loss of commercial or sensitive information (Credit card or personal data etc.)
How to Build a Railway Cyber Defense Plan
A good cyber defense plan for railway companies should consider the following:
– Develop strong governance for rail cybersecurity in the organization.
– Managing and monitoring systems and procedures, to ensure early warning of a cyber-attack.
– Decrease the likelihood of an attack through a multi-layered design and robust operational and maintenance procedures.
– The ability to investigate the attack, after it accrued.
– Force railway suppliers to develop signaling systems that are cyber-secured “by design”.

